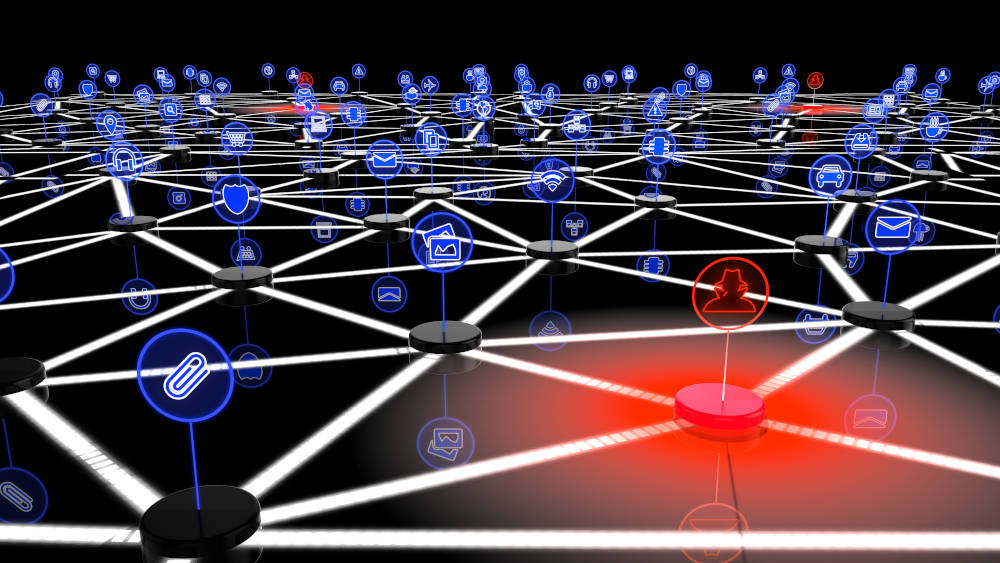
Malware Seeks to Turn Your Computer to a Bot
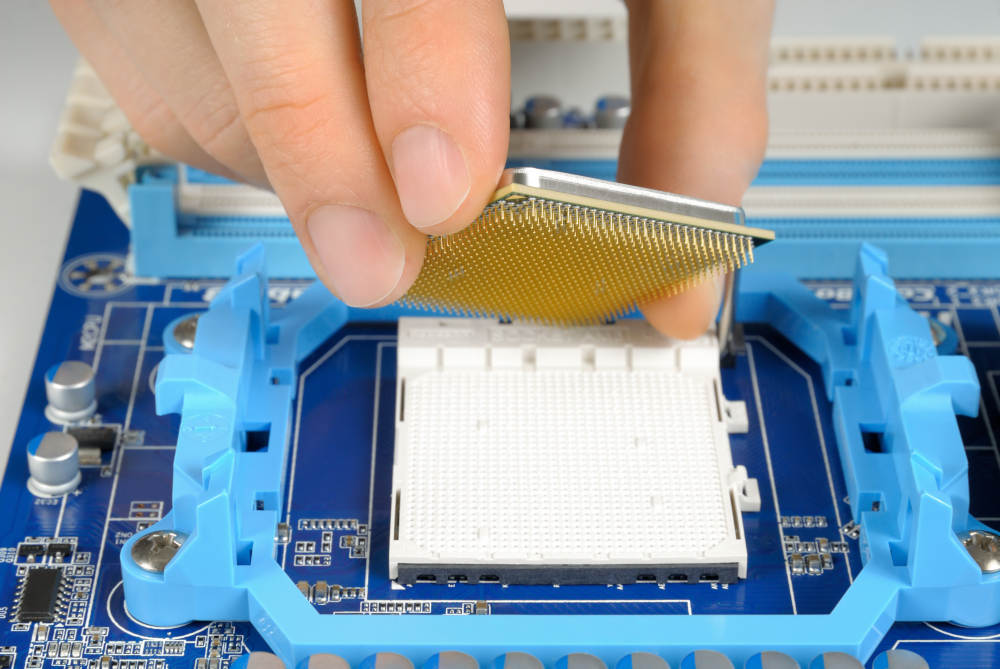
A Plus Computer provides updates on the dynamic world of malware. Malware, viruses, spyware, and adware are terms most of us are acquainted with. Be ready for botnets now. A bot is a single computer that has been compromised and starts operating under the control of the hacker. A group of compromised computers that are…
Read article