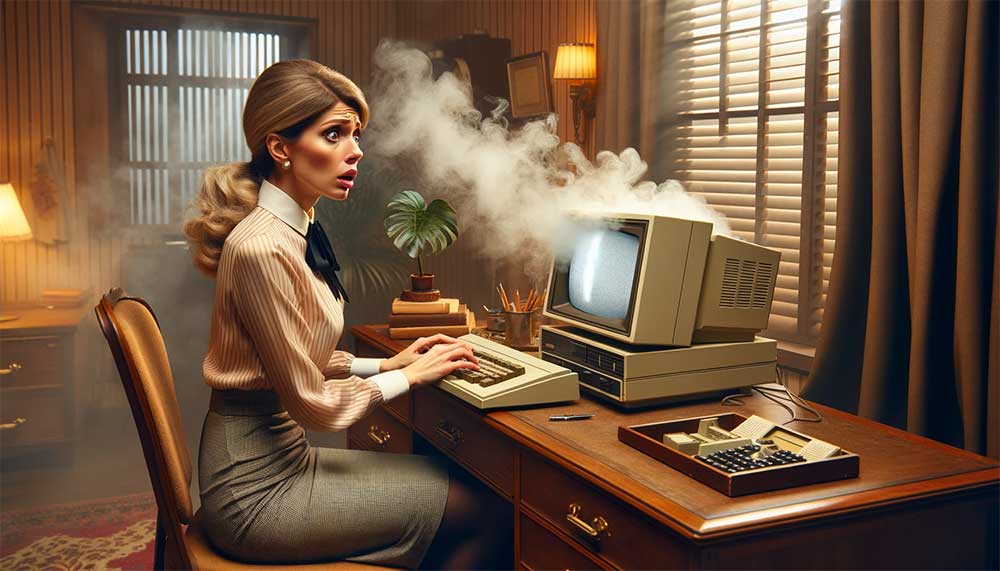
Boost Your Productivity by Upgrading Your Computer or Purchasing a New One
In today’s fast-paced world, productivity is key to success, whether you’re working from home, running a business, or simply managing daily tasks. One of the most significant factors that can affect your productivity is the performance of your computer. An outdated or underperforming machine can slow you down, cause frustration, and ultimately hinder your efficiency.…
Read article